Introduction
In a digital world where security and user convenience are paramount, the concept of Single Sign-On (SSO) reigns supreme. Imagine a world where you no longer need to juggle an ever-growing list of usernames and passwords for various applications and services. Instead, with a single set of credentials, you gain access to everything you need seamlessly. That’s the magic of SSO, and today, we’re going to take you on a journey to demystify how it works, particularly in the realm of Security Assertion Markup Language (SAML).
In this technological adventure, we’ll explore the intricate dance between two powerful entities: Okta, your Identity Provider, and Splunk, the treasure chest of data and insights. We’ll guide you step by step through the process of setting up SSO with SAML, ensuring not only enhanced security but also a smoother user experience. So, fasten your seatbelts and prepare to embark on a quest to simplify login hassles, fortify your digital defenses, and unlock the world of efficient access management. Welcome to the world of SSO with Okta and Splunk—a journey towards a safer, more seamless digital future.
Single Sign-On(SSO)
Single Sign-On (SSO) is a secure authentication process that allows users to access multiple applications or services with a single set of login credentials. Instead of remembering separate usernames and passwords for each application, SSO streamlines the login experience by granting access to all authorized systems after a single login.
Why SSO?
- Enhanced User Experience: SSO simplifies the login process for users, reducing the need to remember multiple passwords and login details. This results in a more convenient and user-friendly experience.
- Improved Security: SSO enhances security by centralizing user authentication and access control. It allows for stronger authentication methods, such as multi-factor authentication (MFA), and ensures consistent security policies across applications.
- Reduced Password Fatigue: SSO significantly reduces the risk of password-related issues, such as forgotten passwords or password reuse, which can lead to security vulnerabilities.
- Efficient Access Management: IT administrators can efficiently manage user access permissions and instantly revoke access when necessary, reducing the risk of unauthorized access.
- Cost Savings: SSO can lead to cost savings by reducing the number of support tickets related to password resets and account lockouts.
When to implement SSO?
Implementing Single Sign-On is beneficial in various scenarios;
- Multiple Applications: When an organization uses multiple applications or services, SSO simplifies user access across these platforms, enhancing productivity.
- Security Requirements: When stringent security measures are essential, such as in industries like healthcare, finance, or government, SSO with strong authentication provides robust protection.
- User Convenience: When user convenience is a priority, SSO reduces friction during the login process, leading to higher user satisfaction.
- Reducing Password-related Issues: When an organization faces challenges related to forgotten passwords, password resets, or security breaches due to weak passwords, SSO can be a solution.
- Centralized Access Control: When there is a need for centralized access control and rapid user provisioning/deprovisioning, SSO simplifies user management.
SAML
SAML, or Security Assertion Markup Language, is an XML-based standard for securely exchanging authentication and authorization data between different parties, such as an identity provider (IdP) and a service provider (SP). It is commonly used for implementing Single Sign-On (SSO) solutions, allowing users to access multiple applications and services with a single set of credentials. SAML ensures the secure transfer of user identity and attribute information, enhancing security and user convenience in authentication processes.
Flow of SAML based SSO
- User tries to access a resource on the Service Provider without being authenticated.
- Service Provider generates a SAML request and redirects the user’s browser to the Identity Provider’s SSO service.
- Identity Provider authenticates the user (e.g., using a username and password) and creates a SAML assertion.
- Identity Provider sends the SAML assertion back to the user’s browser, which then sends it to the Service Provider.
- Service Provider validates the SAML assertion’s digital signature, checks its contents, and grants access to the user.
- User is now authenticated and can access the requested resource.
Okta & Splunk Integration:Step-by-Step Guide
Single Sign-On (SSO) with Security Assertion Markup Language (SAML) streamlines user authentication and access management across different platforms. In this guide, I’ve outlined the step-by-step process to set up SSO between Splunk and Okta.I utilized Okta as the Identity Provider (IdP), but the configurations are applicable to various other Idp services with similar setup requirements.
Add and Configure Splunk plugin in OKTA
- Go to your Okta admin portal, click Applications > Browse App Catalog, and search for “Splunk Enterprise”.
- Select the Splunk Enterprise and click Add integration.
- It opens a configuration tab where you can configure your Splunk Enterprise to Okta.
- In General Setting tab enter Application label (ex. Splunk Enterprise).
- Then enter the Splunk Enterprise site URL (ex.http://127.0.0.1:8001/) in Your site URLand the click Next.
Please keep this Splunk configuration page open, as you will need to revisit it multiple times throughout this procedure.
Retrieve the certificate from Splunk
- Open Splunk Enterprise with Administrator privileges.
- Click Settings select Authentication methods (under USERS AND AUTHENTICATION).
- Select SAML and then click Configure Splunk to use SAML.
- A pop-up appears. Click Download File to download Splunk’s SP metadata. When setting up SAML with any application, metadata needs to be exchanged between the identity provider (Okta) and the SP, or application (Splunk).
- Open this XML file in Notepad++ or another text editor.
- Copy and paste the content enclosed within the <ds:X509Certificate> tag (the string inside the XML tags) to a new text file, prepending and appending —–BEGIN CERTIFICATE—– and —–END CERTIFICATE—– as shown here.
- Save the file as splunk.cert.
Configuring Okta Single Logout (SLO)
- In Okta, select the Sign-On Options tab from Splunk Enterprise integration.
- Default Relay State -the Default Relay State for Okta SAML integrations with applications like Splunk is left empty .
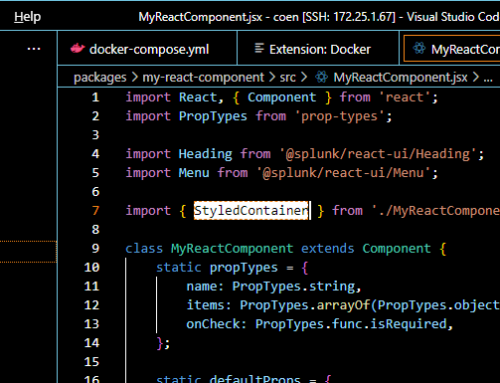
- Set up the “role” configuration. This determines the Okta groups to which a user belongs and is transmitted to Splunk Enterprise through the SAML authentication request. In the example below, it is configured as “Matches Regex” with the value of “.*,” which means to send anything (ex:_. *’).
- Select Enable Single Logout. Single Logout (SLO) is a feature that allows users to seamlessly and securely logout of Splunk Enterprise and Okta at the same time.
- Under Signature Certificate, upload your splunk.cert file.
Incorporating Okta’s metadata into Splunk
- Copy the Metadata URL from Sign On tab and paste it into your web browser. Save the resulting page as an XML file, which is required for uploading in Splunk Enterprise’s SAML Configuration.
- In Splunk’s configuration page, upload this file by choosing Select File in the Metadata XML file field.
Important Note: The Entity ID must be identical on both Splunk Enterprise and Okta, and it must be in string format.
- You will observe that all the empty fields in the SAML configuration tab will now be populated with values.
- Save all configuration.
Mapping Okta groups to Splunk roles
- In Splunk Enterprise,click Settings select User and Authentication
- In SAML settings you can create SAML Groups with respective privileges (Admin, user). click SAML Configuration ,Select New Group.
- Add group mappings. You can add multiple mappings and also map multiple Splunk roles to one Okta group.
- Assign a user to the app in Okta and test it out.
- Users can now effortlessly access a Splunk deployment through the Okta portal using their Splunk accounts, eliminating the need to remember or utilize Splunk passwords.
NOTE:
- If an issue arises, log in as a regular Splunk user by visiting:
http(s)://<your_server>:8000/en-GB/account/login?loginType=Splunk - Splunk roles are automatically assigned based on the corresponding Okta groups.
- Before assigning groups or individual users to Splunk Enterprise, it’s essential to create users and groups in Okta (IDP). You can find detailed instructions on how to create users and groups in Okta by following this link https://help.okta.com/en-us/content/topics/users-groups-profiles/usgp-add-users.htm
Testing SAML Configuration
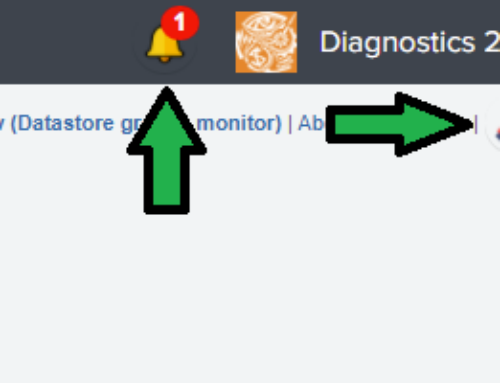
To verify the SAML configuration, try launching the Splunk Enterprise application. Doing so will prompt the appearance of the Okta login page. Enter the login credentials that you’ve previously set up in Okta and assigned to Splunk Enterprise.
if you’ve managed to log in to the Splunk application without any issues, you can now confirm that the SAML is operating as intended.
Troubleshooting Common Isues
If you encounter errors such as ‘SAML response lacks group information‘ while accessing the application. it is due the SAML response from the Identity Provider (IdP) does not include the necessary group information or attributes required by the Service Provider (SP).
Here are some common reasons for this error:
- Attribute Mapping: In an SSO setup, the IdP needs to include attributes in the SAML response that provide information about the user, including their group memberships. If the attribute mapping between the IdP and SP is not correctly configured, the group information may not be included in the SAML response.
- IdP Configuration: The IdP must be configured to release the group attributes or roles associated with the user to the SP. This configuration can vary depending on the IdP used and it’s essential to ensure that the necessary attributes are being included in the SAML response.
- Group Information in SAML Response: The IdP may not be configured to include group information in the SAML assertion or response. It’s crucial to review the IdP’s SAML configuration settings to ensure that group information is included.
- SP Configuration: On the SP side (the service/application you’re trying to access), there should be a corresponding configuration to map the incoming SAML attributes to roles or groups within the application. If this mapping is not set up correctly, the application may not recognize the group information.
- Role Mismatch: Ensure that the roles or group names in the IdP match the roles or group names expected by the SP. If they don’t match, the SP won’t be able to recognize the group information provided by the IdP.
- Testing and Troubleshooting: Thoroughly test the SSO flow and review logs and error messages on both the IdP and SP sides to identify any specific issues. Logs can often provide more detailed information about the cause of the error.
- Attribute Release Consent: In some cases, users may need to grant consent for the release of certain attributes, including group information. Ensure that users have provided consent for this data to be shared.
- SAML Response Format: Check if the SAML response format (e.g., SAML 2.0) is compatible between the IdP and SP. A mismatch in SAML versions or configurations can lead to attribute-related issues.
Conclusion
Implementing Single Sign-On (SSO) using Security Assertion Markup Language (SAML) between Okta and Splunk offers significant benefits, including enhanced user experience, improved security, and streamlined access management. This step-by-step guide outlines the process for configuring SSO, ensuring a seamless and secure authentication experience for users across these platforms while minimizing the risk of password-related issues.
Sanjai S
Software Developer
sanjai@redplanet.com.my




















Leave A Comment